
Asymmetric Frontiers: Strategic Fortifications for Global Finance Against State-Sponsored Persistent Threats
 RN
RNThe global financial landscape is currently undergoing a paradigm shift, transitioning from traditional perimeter-based security to a state of constant, "active defense" in response to an unprecedented surge in state-sponsored cyber operations. Groups linked to the Reconnaissance General Bureau of North Korea (DPRK) and the Islamic Revolutionary Guard Corps (IRGC) of Iran have moved beyond mere data exfiltration, evolving into sophisticated actors capable of manipulating market dynamics. For banks, insurers, and institutional investors, the threat is no longer confined to the loss of customer records; it has escalated into a structural risk targeting the integrity of sovereign debt markets and the stability of corporate valuations.
Current intelligence suggests a strategic divergence in methodologies. While Iranian-linked Advanced Persistent Threats (APTs) have intensified their focus on disruptive signaling—utilizing social engineering and the manipulation of Programmable Logic Controllers (PLCs) to impact infrastructure—North Korean actors remain primarily motivated by financial gain to circumvent international sanctions. These entities are now deploying "agentic" attack speeds, using automated AI-driven scripts to exploit zero-day vulnerabilities in financial software supply chains. The risk is compounded by the "Lazarus" methodology, which increasingly targets decentralized finance and traditional banking gateways to extract liquidity.
The vulnerability of the financial sector is particularly acute in the realm of market manipulation. Hackers are moving toward schemes that target the "data integrity" of trading platforms. By executing subtle, unauthorized modifications to high-frequency trading algorithms or disseminating deepfake-driven misinformation, these actors can trigger artificial price volatility. For major enterprises, this translates into "valuation erosion," where stock prices can plummet significantly within days of a suspected breach. Even more critical is the systemic threat to the bond market. If a nation-state actor successfully compromises the clearing and settlement systems for sovereign risk instruments, the resulting uncertainty could lead to a catastrophic spike in yields or a complete freeze in liquidity for infrastructure financing.
To mitigate these risks, financial institutions must implement a Zero Trust Architecture (ZTA) that assumes a breached state at all times. This requires micro-segmentation of critical networks to prevent lateral movement and the adoption of "Active Cyber Defense" protocols. These protocols involve real-time threat hunting and the use of quantum-resistant cryptography to protect long-term sovereign assets. Furthermore, insurers must integrate "Risk-Based Security Theory" into their underwriting, prioritizing the protection of "Data Trust" over mere "Data Privacy." As geopolitical tensions continue to manifest in the digital theater, the survival of the global financial order depends on the ability of its primary actors to transition from static, reactive defenses to an architectural resilience that can withstand the asymmetric weight of nation-state aggression.


Fortalecimiento de los sistemas de vigilancia y mitigación ígnea en el territorio cordobés

Gestión de Riesgos Subnacionales: El Salto Hacia un Paradigma de Resiliencia Financiera en Argentina
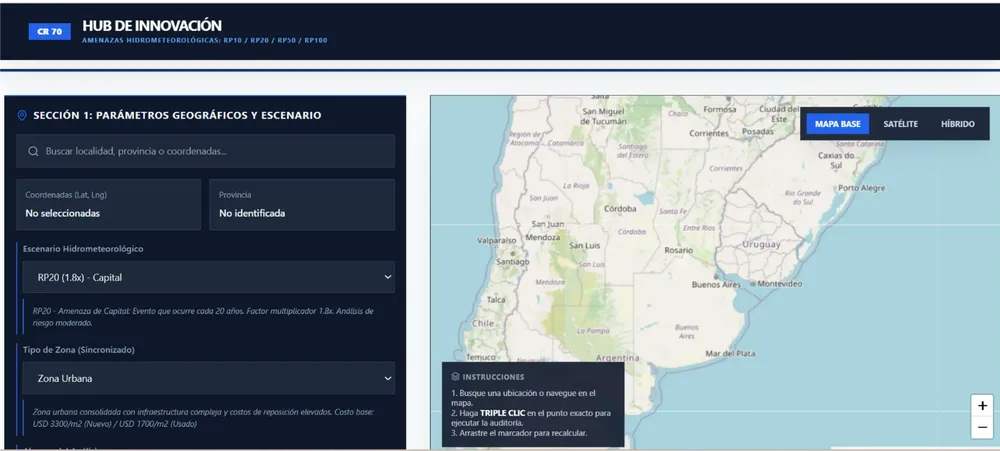
Resiliencia Financiera y Gestión del Riesgo: La Innovación en el Cálculo del Costo de Reposición de Infraestructura Crítica en Argentina

Guerra Híbrida: El Frente Digital que Amenaza con Paralizar el Mundo Real

El Desafío Invisible: ¿Están los Parques Industriales Argentinos Listos para una Catástrofe Química?

El equilibrio lumínico en la seguridad vial: ¿Es la luz blanca siempre superior?

Gestión de Riesgos Subnacionales: El Salto Hacia un Paradigma de Resiliencia Financiera en Argentina

El dilema de la infraestructura: La estrategia de máxima presión sobre el Golfo Pérsico

Asymmetric Frontiers: Strategic Fortifications for Global Finance Against State-Sponsored Persistent Threats
